From Sea Power to Cyber Power: What CISA Could Learn From Mahan
All Views in this newsletter are my own and do not represent the views of The R Street Institute, the US Navy, or any other organization I am affiliated with.
This week, I'm channeling James Holmes from the U.S. Naval War College. I will no doubt come up short, but I wanted to tip my hat to one of the greats.
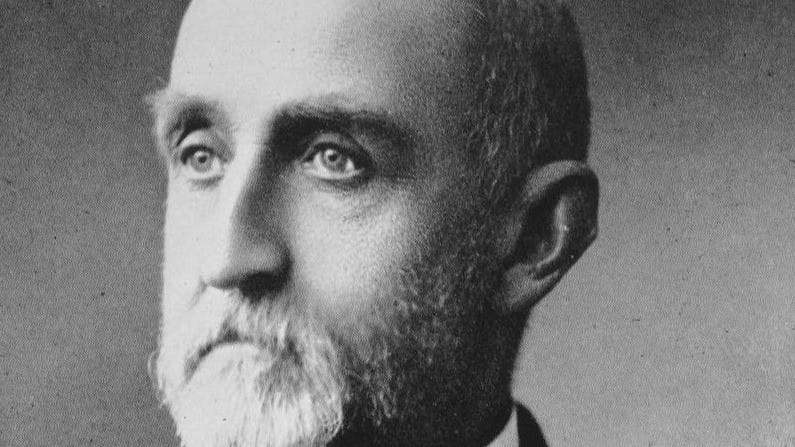
Alfred Thayer Mahan's The Influence of Sea Power Upon History revolutionized naval strategy and inspired its readers, such as Teddy Roosevelt and Kaiser Wilhelm II. Within the book, Mahan advocates for a strong Navy as a necessary condition for having a great nation. He also highlights one key strategic insight for controlling the global commons that is the sea: secure strategic chokepoints, don't try to control everything. Focusing on the Suez Canal, Gibraltar, and Panama Canal is sufficient to protect commerce and project power.
During the Cold War, the Soviet Navy made the exact strategic error Mahan warned against. Divided into four fleets, separated by vast distances, the Soviet Navy could not concentrate and disperse its forces as needed. Soviet naval strategy violated every principle of concentration that Mahan advocated. This was not a strategic blunder, but a consequence of geography. The Soviets were forced to defend everything, and as a result, they could control nothing decisively. As put by Hanson Baldwin in the Summer 1955 edition of Foreign Affairs, "Geography is the Russian Navy's undoing."
Today in cybersecurity, the US is making the same strategic error that the Soviet Navy did. We are ignoring Mahan's fundamental principle, albeit by choice rather than geographical necessity. Instead of focusing on defending cyber chokepoints, we're trying to protect everything labeled as "critical infrastructure," applying that designation extremely liberally.
The Cybersecurity and Infrastructure Security Agency (CISA) is the national cyber defense agency of the United States. They have designated 16 "critical infrastructure sectors whose assets, systems, and networks...are considered so vital to the United States that their incapacitation or destruction would have a debilitating effect on security, national economic security, national public health or safety".
CISA's mission is to protect these critical systems through coordinated federal cybersecurity efforts, and its work is essential. The problem lies in what they consider critical infrastructure, whose incapacitation would have a debilitating effect on national security, economic security, public health, or safety. Comparing two of the critical infrastructure sectors (the commercial facilities sector and the nuclear reactors, materials, and waste sector) highlights the problem with this approach. Shopping malls have the same critical designation as nuclear power plants and are eligible for the same vulnerability scanning and risk assessments.
When everything is critical infrastructure, nothing is critical infrastructure. This is strategic sprawl disguised as comprehensive protection. If the British Royal Navy in 1914 operated like this, it would have been trying to patrol every harbor instead of controlling key straits. The German High Seas Fleet would have been able to overpower the Royal Navy and defeat it in detail rather than remaining in port, which could have turned the tide of World War I.
CISA conducted "over 9,400 engagements" in 2024, including "3,900 with healthcare, 3,400 with water entities, and more than 2,000 with schools." These are commendable numbers, but they show that we are spreading cybersecurity expertise across thousands of entities with questionable strategic value. Small municipal water systems receive the same federal attention as major hydroelectric dams, while individual K-12 schools receive cybersecurity assessments that should be reserved for strategic facilities.
The Trump administration is taking steps that would exacerbate the problem. Proposed budget cuts are forcing exactly the choice Mahan warned against. Trump's proposed fiscal 2026 budget would cut "$495 million and nearly 30% of positions" at CISA while maintaining the same sprawling 16-sector critical infrastructure mandate. This would pile on to a current staffing problem, as a third of CISA's workforce has already left the agency through voluntary buyouts, early retirement, or layoffs.
The good news is that real cybersecurity chokepoints exist and Mahan would recognize them. DNS root servers control global Internet name resolution. If compromised, websites become unreachable worldwide. Payment clearing systems such as Visa and Mastercard process the majority of electronic transactions. Their failure would freeze commerce within hours. Major electrical grid interconnections transfer power across regions. Successful attacks could trigger cascading blackouts affecting multiple states.
These systems create the strategic dependencies Mahan understood. Unlike shopping malls, their failure generates genuine cascading effects across multiple sectors simultaneously. A coordinated attack on payment systems and electrical interconnections could paralyze the economy more easily and effectively than destroying every retail center in America.
There's a naval historical case that demonstrates Mahan's theories in practice. In 1904, well before the start of World War I, First Sea Lord Jackie Fisher implemented reforms that exemplified strategic concentration. Facing a significant German naval threat, he withdrew British ships from global patrol duty to concentrate them in home waters. He chose strategic focus over comprehensive coverage, and as a result, Britain maintained its naval supremacy.
CISA should apply the same principle: excellently defend 50 genuine chokepoints rather than poorly defend 5,000 shopping malls. The agency's finite cybersecurity expertise belongs where failure creates systemic risk, not bureaucratic completeness.
What This Means For...
Policymakers: Stop designating everything as "critical infrastructure." CISA needs to focus federal resources on genuine chokepoints, such as DNS root servers, payment clearing systems, and major electrical grid interconnections, rather than spreading expertise across shopping malls and individual schools. Evidence-based prioritization, not bureaucratic comprehensiveness, should drive cybersecurity policy.
U.S. strategic competition: Our current approach hands adversaries a strategic advantage. While we dilute resources across thousands of "critical" facilities, competitors can focus on the genuine chokepoints we're neglecting. China doesn't need to attack every designated critical infrastructure sector. It only needs to target the dependencies that actually matter.
Critical infrastructure operators: Prepare for a drop in CISA support, because it's coming. Don't assume federal designation equals federal protection. Develop internal cyber resiliency rather than waiting for CISA assessments. The agency's finite resources are already spread too thin to provide meaningful security to everyone carrying the "critical infrastructure" label.
Aspiring strategic thinkers: Mahan's principle of strategic concentration remains as relevant today as it was a century ago and can be applied outside of the naval domain. When resources are finite (when aren't they?), strategic focus always beats comprehensive coverage. Learn to distinguish between what looks important and what actually creates cascading failure when it breaks.